There is a LOT of content on the internet. In fact, as of July 22nd, there are 5.93 billion indexed web pages. That’s a lot of content.
One of the biggest challenges faced by contemporary content creators is getting their content viewed. In order to achieve this, many individuals and organizations are spending time and money devising new and innovative ways to go viral.
However, gaining visibility in an increasingly crowded cybersecurity marketplace is easier said than done. There exists online a plethora of individuals and organizations well versed in creating content that attracts visitors to their site (instead of a competitor’s) in order to sell products or services. These individuals and organizations utilize a myriad of ways to drive people to your site including social media, email, PPC, and of course, SEO – the list goes on.
But still, despite having all these tools at their disposal, many fall at the first hurdle. So the question remains – how do you actually come up with viable ideas that your customers, prospects, and the cybersecurity community will want to read?
Let’s take a look…
Think about your business objectives.
This is the best place to start. What are your company’s aims and objectives for the year? What products do you sell? What industry needs are you meeting? Simply have a look at what solutions you sell, and align your topics to that. If your topic is application security, for example, you obviously need to create content around that. If your topic concerns the cybersecurity industry’s much-publicized skills gap, and how to help resolve this issue, a good idea might be to highlight the process of machine learning and other related processes. A good starting point is to take a look around your own homepage and on the most prominent pages on your website compose a list of those keywords.
What is popular in the world of cybersecurity and beyond?
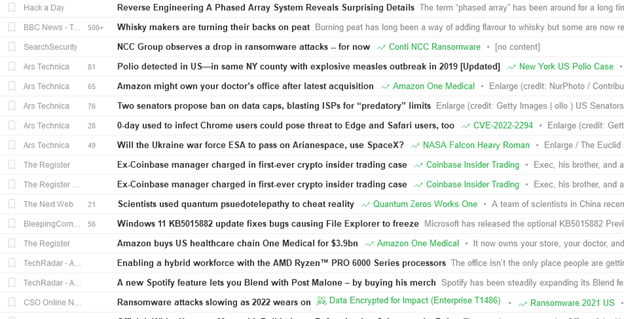
In order to effectively gauge what is popular, you need to aggregate the latest industry news and identify the most prominent issues. In order to achieve this successfully it is advisable to use a news aggregator application such as Feedly. Using a tool like Feedly allows you to keep updated as to what topics are trending, getting frequently shared, and being actively engaged with by potential customers. A useful feature on Feedly is that you can see the number of times things have been shared, as Feedly highlight key topics in green to ensure they stand out:
You can use tools like Google Trends to see what the rest of the world is talking about and craft curated content that is aligned to those popular topics. If it’s a football World Cup year, for example, you might want to write an article entitled: “5 Cybersecurity Concerns around Qatar’s 2022 World Cup”, or it could be Black Friday and you want to write something like, “Black Friday Sale: 5 Tips to Stop Getting Scammed” or something similar to that. One top tip is to type in your keywords and see how they are trending and see if you should be actually covering topics.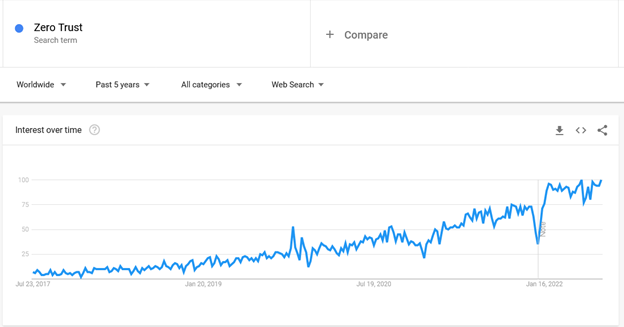
Review your old content
One of the best ways to come up with new ideas, whilst actually helping improve the health of your site and domain authority, is to actually look back and review what content you’ve already published. Utilizing tools like Animalz Revive allows you to see what articles are starting to drop in ranking and views – so you might want to prioritize updating them first. Alternatively, have a look and see what is popular with your readers and look to cover more content that is aligned to that topic. If it’s already working, look to take advantage of that and structure your content accordingly.
Search Engines
Google is a great source for coming up with new ideas. For most sites, it’s pretty typical that a majority of their traffic comes from search engines, so take a look at what they are serving up and do your research there.
If you’re looking to cover API Security, start typing it into Google and see what appears: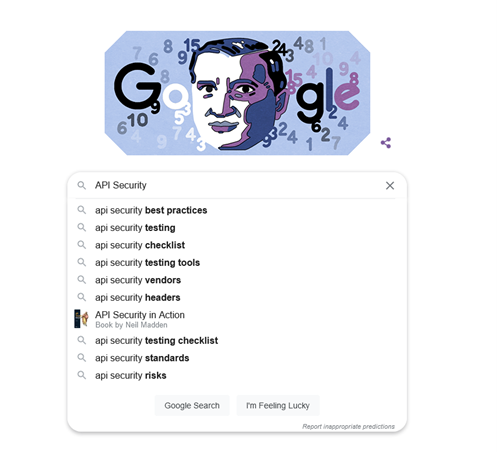
The suggestions presented by Google reveal the things other people are searching for. These are popular phrases. If you want to go deeper, you can add each letter next to the term and see what comes up. For example,
API Security a
API Security b
API Security c
Google is also just a great place to search for terms and see what other content has been covered on the topic. You can review it, draw inspiration from it and look to create something even better!
Tip: If you change your VPN location, you get to see localized results. Might be worth doing this for specific countries you are targeting.
Attend Events
Industry events are a great place to go to learn and discover more information about trending cybersecurity topics. Whether it’s something global like Black Hat, or a localized BSides event – attend sessions and engage with vendors to see what topics leading industry insiders are speaking about. Attendance at such events will give you a huge list of potential ideas and whilst you’re there, you can network with speakers and possibly even gain quotes and other contributions for your own content!
Ask your team/customers for content ideas
If you’re part of a cybersecurity marketing team and struggling for relevant ideas – then dip into your existing talent pool and ask them for their ideas. Talk to your sales department. What are customers talking about? What are their biggest concerns? You can look to write about some of those topics. Not only will your colleagues have a unique insight, but you can actually assist your team in creating content that resonates with their peers, and they will hopefully use it as a tool to nurture prospects. Don’t stop with sales either- talk with R&D, engineers, and product managers.
Dive into your products
Talking to product managers can provide you with a real sense of some of the key features and benefits of your tools and solutions. If you’re selling a configuration management solution and one of the main features is it helps eliminate configuration drift, why not write a blog on it? It might not have the same search volume or mass appeal as some topics, but it’s important to your business and your customers.
Social Media
Another place you can look for ideas is on social media. Ensure you follow prominent content creators who are authority figures in the space to see what topics they are talking about now, and what they signpost as being key things to keep an eye on for the future. Construct and continually update lists of influential individuals and organizations in the space – what are they sharing? Look at influencers, brands, and your connections. What are they talking about, discussing, and sharing? You could even be so bold as to ask some of your peers what they want to see being covered.
Now we’ve come up with a few ways of finding topics to cover, you have to be creative in coming up with specific titles and ideas to bring these ideas to life.
Coming up with titles
A big challenge for a lot of Marketing teams is to turn these identified topics into creative ideas. What type of titles will drive engagement but also help with SEO and provide longevity?
Personally, I like that adopt a few different styles. Here are a few examples:
Lists:
5 API security best practices
10 DevOps tools to bolster your security stack
How to:
How to apply the Risk Management Framework
How to report a data breach
Tips for:
5 tips when looking for a pentesting service
7 tips for selecting the right tool for your SOC
Questions:
Is there a cybersecurity skills gap?
Is the private or public cloud right for your business?
Timeline:
NotPetya: timeline of a ransomware
Equifax data breach: a timeline of events
Everything you need to know:
Black Basta ransomware: what you need to know
Everything you need to know about FISMA
Tip: It’s even better when you can combine several things together! Something like “6 common phishing attacks and how to protect against them”.
I hope you enjoyed this brief overview of how you can come up with ideas and create titles. Now it’s time to get to work creating your own content.
Are you struggling to find the time? Make sure you contact the team at Bora to learn how they can help to work with you and your business, saving you time and energy so you can concentrate on other marketing tasks.